CacheWarp: A New Vulnerability Affecting AMD EPYC CPUs
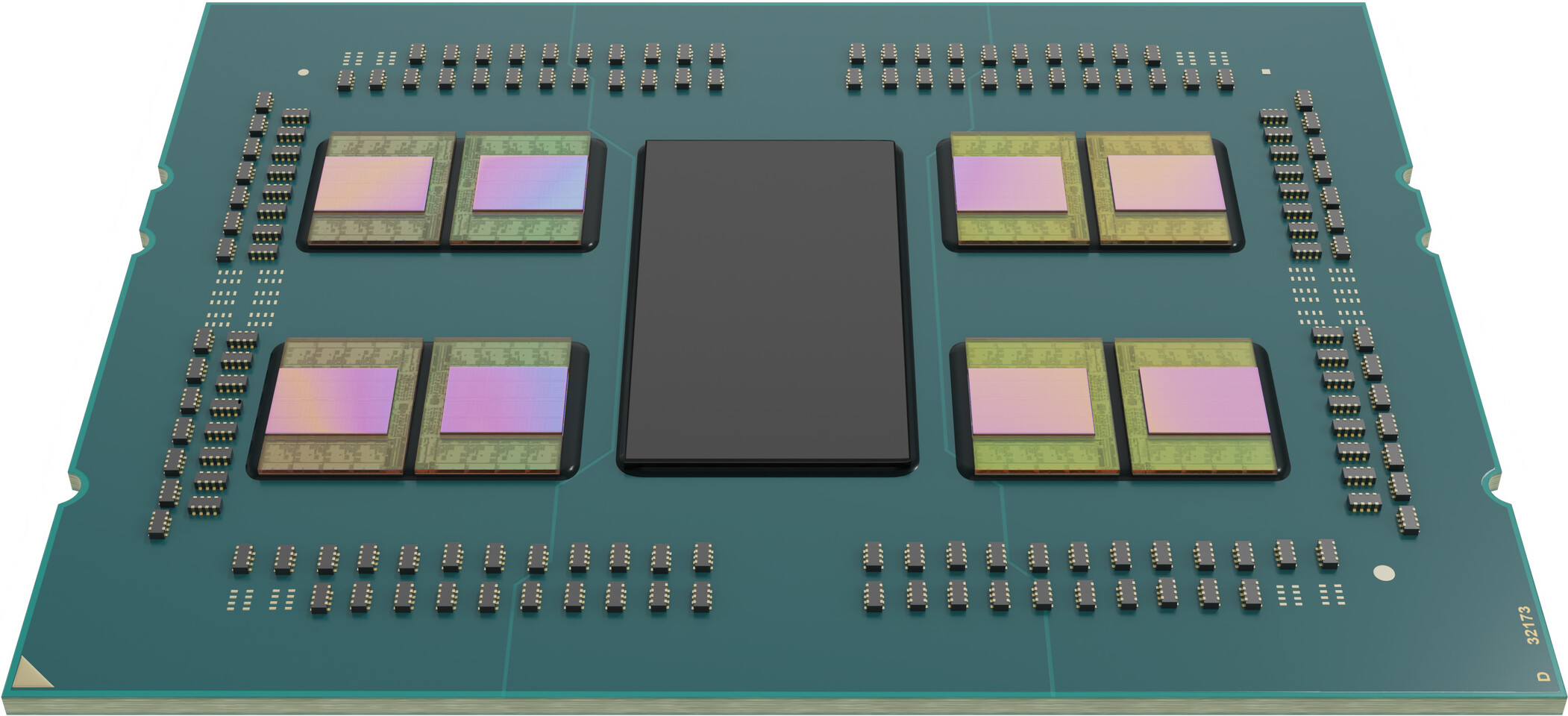
Researchers from Graz University of Technology and the Helmholtz Center for Information Security have recently published a paper on CacheWarp, the latest vulnerability impacting certain prior generation AMD EPYC CPUs. This vulnerability, known as CVE-2023-20592, specifically targets the first-generation EPYC Naples, second-generation EPYC Rome, and third-generation EPYC Milan.
CacheWarp takes advantage of a weakness in AMD's Secure Encrypted Virtualization (SEV) technology, with a focus on the SEV-ES (Encrypted State) and SEV-SNP (Secure Nested Paging) versions. By utilizing a software-based fault injection technique, CacheWarp manipulates the cache memory of a virtual machine (VM) running under SEV. It cleverly forces modified cache lines of the guest VM to revert to their previous state, effectively bypassing the integrity checks enforced by SEV-SNP. This allows the attacker to inject faults without detection.
What sets CacheWarp apart from other attacks is its versatility and danger. Unlike attacks that rely on specific vulnerabilities within the guest VM, CacheWarp exploits the underlying architectural weaknesses of AMD SEV, making it a significant threat to systems that rely on this technology for security. This attack can bypass robust security measures, such as encrypted virtualization, posing a substantial risk to data confidentiality and integrity in secure computing environments.
AMD has taken steps to address this vulnerability. For EPYC Milan, they have released an update with a hot-loadable microcode patch and an updated firmware image. This update does not result in any expected performance degradation. However, for the first and second generations of EPYC processors (Naples and Rome), AMD states that no mitigation is available. This is because the SEV and SEV-ES features were not designed to protect guest VM memory integrity, and SEV-SNP is not available.